USB-C Authentication Tech to Restrict Usage of Uncertified USB-C Accessories and Cables
by Anton Shilov on April 13, 2016 10:30 PM EST
The USB Implementers Forum has announced a new addition to the USB Type-C specification, which is projected to restrict usage of uncertified or potentially malicious accessories with reversible USB-C connectors. The USB Power Delivery 3.0 specification contains a special extension called, the USB Type-C Authentication specification, which promises to help host devices to identify chargers, cables, storage solutions and hosts before making connections. However, to take advantage of the tech, new devices will be needed.
USB interconnections are expected to get more popular than ever thanks to convenience of reversible USB Type-C, its ability to deliver up to 100W of power and support for custom features. However, expanded functionality requires more sophisticated cables with multiple wires and special ID chips, which are more expensive to make than traditional USB cables. As it turned out in the recent months, many cheap cables are not compliant with USB-IF’s requirements; they either do not support high data-rates, cannot charge USB-C devices, or may even damage products they are connected to. The USB authentication promises to end frustrations and make future USB-C devices a little more secure, as an added bonus.
Devices compliant with the USB PD 3.0’s USB-C authentication tech will be able to verify capabilities of accessories compliant with the authentication technology and whether or not they have been certified by the USB-IF. The verification information will be exchanged right after devices are connected, before any data or energy is transferred. The USB-IF will make it possible to set up policies that will restrict usage of incompatible or uncertified accessories with particular host devices.
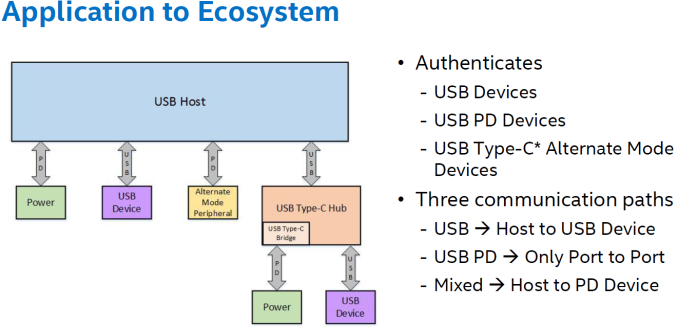
The USB-C authentication will divide accessories into three types: USB devices, USB power delivery devices (e.g., chargers) and USB Type-C alternate mode devices (e.g., displays). The authentication data messages will be transmitted using different communication paths (USB bus, USB PD or mixed) and will be encrypted using 128-bit methods.
| USB Type-C Authentication Cryptographic Methods | |
| Method | Use |
| Framework (ITU X.509) OID (ITU-T X.402) DER-encoding (ITU-T X.690) |
Certificate format |
| ECDSA (ANSI X9.62) using NIST P-256 curve (NIST-FIPS-186-4) | Digital signing of certificates and authenticationmessages |
| SHA256 (NIST-FIPS-180-4) | Hash algorithm |
| NIST-compliant PRNG source (SP800-90A) seeded with a 256-bit fullentropy value (SP800-90B) | Random numbers |
Based on what is known about the USB authentication, the technology can restrict usage of uncertified cables only in cases their usage is prohibited by manufacturers or end-users users themselves. Moreover, it will only be completely supported by fully-featured cables compatible with the USB Power Delivery 3.0 specifications, which will contain a chip with ID as well as optional vendor defined messages.
According to the USB-IF, it is possible to add the USB-C authentication protocol to host devices by updating their software and firmware, but that will depend on device manufacturers. Since it is not feasible to update things like chargers or cables, they will need to be replaced, or, their usage should be permitted by software-defined security policies. Owners of PCs, tablets and smartphones will be able to authorize only certain accessories to work with their devices, making it impossible to plug a USB flash drive to a host containing confidential data. Nonetheless, once an accessory is authorized, it will be able to work with hosts, harm them or even infect them with viruses. Therefore, the new USB technology is not a replacement for antiviruses.
It remains to be seen how different manufacturers take advantage of the new technology. If implemented too strictly, some hosts may get incompatible with the majority of cheap USB-C products on the market.
At present we do not know when the USB-IF plans to start certification of devices with the USB authentication technology and how the organization plans to certify thousands of cables and chargers. Perhaps, Intel, the company that developed the USB PD 3.0, will reveal more information at its IDF trade-show in the coming days, so, stay tuned.
Source: USB-IF (via Ars Technica)
















28 Comments
View All Comments
Howard - Wednesday, April 13, 2016 - link
"Tpe-C"Ryan Smith - Thursday, April 14, 2016 - link
Tpe-OWithoutWeakness - Thursday, April 14, 2016 - link
Took me a second to realize how clever this reply was.Trackster - Thursday, April 14, 2016 - link
This reply is gold.p1esk - Thursday, April 14, 2016 - link
I didn't get it...paddytokey - Friday, April 22, 2016 - link
Typo (a typing error)wolfshades - Monday, April 18, 2016 - link
Wish this place had upvotes or something. This comment deserves it.barleyguy - Thursday, April 14, 2016 - link
Hacking for interoperability was made legal under case law in the Lexmark case. So this will be hacked, legally, probably a week after it's released. Kinda makes it pointless IMO.ZeDestructor - Thursday, April 14, 2016 - link
No hacking needed. All you need is to get your cert signed by USB-IF (or self-sign and install your root CA on all machines you plan to use your custom stuff on). It's all very TLS/SSL-like, and I personally feel that that's a very positive thing.Oh, and if you work in an environment where you need to restrict USB devices due to security/privacy/trade secret knowledge (like, say, a bank), you can install your own certs to USB cables and devices like thumbdrives, and only allow those to connect fully. Meanwhile, everything else, like phones, can just sit around in power-only mode.
ZeDestructor - Thursday, April 14, 2016 - link
Source: I read the bloody spec.